When you send Bitcoin or Ethereum, it doesn’t vanish into thin air. Every transaction is recorded forever on a public ledger. That’s the core idea behind on-chain crypto transaction tracing. It’s not magic. It’s math, patterns, and data analysis. And it’s how investigators find stolen funds, track ransomware payments, and help exchanges stay compliant with the law. But it’s not foolproof. Understanding how it works - and where it falls short - is key to knowing what’s really possible.
How On-Chain Tracing Actually Works
Blockchain networks like Bitcoin and Ethereum are public. Anyone can see every transaction ever made. That’s the foundation. But wallets don’t have names. They have long strings of letters and numbers. So how do you connect a wallet to a real person? You don’t. Not directly. Instead, you look for patterns. One of the most common techniques is address clustering. Imagine you see five different wallets sending small amounts to one central wallet every day. That’s not random. It’s likely one person or business using multiple addresses to hide their activity. Tools like Nansen and Elliptic use algorithms to group these wallets together into clusters. If one wallet in that cluster is linked to a known exchange account (say, through KYC data), then suddenly, all the others in the cluster become suspect. This isn’t guessing. It’s pattern recognition based on real-world behavior. Another method is common spend analysis. If two wallets send funds to the same third wallet at the same time, they’re probably controlled by the same entity. Why? Because it’s inefficient to coordinate multiple people to send money together unless they’re working as a team. This is especially useful when tracking stolen funds that get split up and sent to multiple destinations. Then there’s address reuse. People think using a new address for every transaction keeps them private. But many don’t. If a wallet is used more than once - say, to receive a payment and later to send change - that’s a clue. It’s like using the same credit card for groceries and then withdrawing cash. It links two activities.The Tools That Make It Possible
You can’t do this with a browser alone. You need specialized tools.- Blockchain explorers like Etherscan and Blockstream let you view raw transaction data. They’re free and open, but they only show the surface.
- Professional analytics platforms like Nansen, TRM Labs, and Chainalysis Reactor combine transaction data with external information - exchange registrations, known criminal addresses, token flows - to build visual maps of fund movement.
- Open-source tools like BlockSci are used by researchers and advanced analysts who want to build custom models. They’re powerful but require serious technical skill.
What Happens When Money Crosses Chains?
This is where tracing gets messy. In 2024, over 40% of illicit crypto transactions involved at least two different blockchains. A thief might steal ETH on Ethereum, swap it to BNB on Binance Smart Chain, then move it to Tron, and finally convert it to USDT. Each hop is a new puzzle. Cross-chain bridges are the weak link. They lock one token on Chain A and mint a new version on Chain B. Investigators need to understand how each bridge works. Some use centralized custodians. Others use smart contracts. If you miss the bridge logic, you lose the trail. Tools like TRM Labs and Nansen now offer automated cross-chain tracing. They track how funds move through bridges, even if they jump between 3 or 4 networks. But accuracy drops. Heuristic methods (simple rule-based tracing) fall to 63% accuracy across chains. Even advanced tools struggle when the trail goes cold on obscure networks like Solana or Avalanche.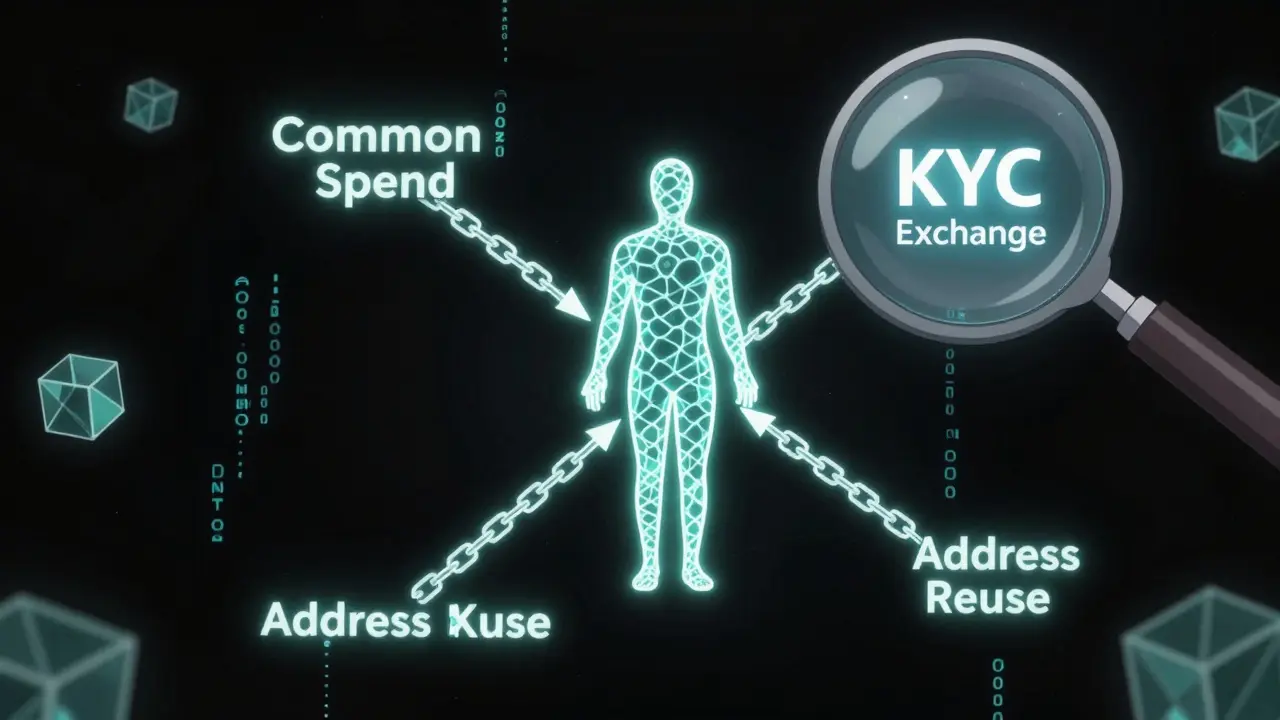
Limitations: Where Tracing Fails
No matter how advanced the tools, on-chain tracing has hard limits. First, pseudonymity isn’t anonymity. Wallets aren’t tied to names. But that doesn’t mean they’re invisible. Still, without external data - like a KYC-verified exchange account or an IP address leak - you can’t prove who owns a wallet. You can only say, “This cluster of wallets behaves like one entity.” Second, privacy coins like Monero and Zcash are designed to break tracing. In 2024, they accounted for 7.2% of all illicit transaction volume. Unlike Bitcoin, they hide sender, receiver, and amount. There’s no public trail. Tracing them requires entirely different methods - if it’s even possible. Third, mixers and decentralized protocols like Tornado Cash (which was shut down but still active on forks) shuffle funds between hundreds of wallets. It looks like a maze. In 2024, mixers were used in 18.3% of all criminal crypto flows. Even the best graph-learning tools can’t reliably untangle them.Who Uses This and Why
This isn’t just for cops. It’s for banks, exchanges, and regulators. The Financial Action Task Force (FATF) made blockchain tracing mandatory in 2019. Their “Travel Rule” says exchanges must share sender and receiver info for transfers over $1,000. To comply, 87% of crypto exchanges now use analytics tools. The European Union’s MiCA regulation and the U.S. Executive Order 14067 pushed this further. By 2024, 63 of the top 100 global banks had implemented blockchain monitoring. For law enforcement, tracing helps recover stolen funds. In 2023, the U.S. Treasury seized $100 million in Bitcoin tied to the Lazarus Group after tracing it through multiple chains. For exchanges, it’s about avoiding fines. The U.S. Treasury fined BitMEX $100 million in 2020 for failing to monitor illicit flows. But it’s not without controversy. Privacy advocates warn that these tools can be misused. The Electronic Frontier Foundation argues that mass surveillance of blockchain data risks chilling legitimate financial activity. If your neighbor sends you $50 in ETH for dinner, should that be flagged? The line between crime-fighting and overreach is thin.







Comments
Mohammed Tahseen Shaikh
March 20, 2026 AT 10:50 AMLet’s be real - tracing crypto isn’t magic, it’s just pattern recognition with a side of corporate surveillance. I’ve seen wallets get clustered because someone reused an address after buying coffee. That’s not a criminal, that’s someone who forgot to use a new one. The tools are impressive, but the assumptions? Wildly overreaching.
And don’t get me started on cross-chain bridges. You think Nansen sees the full picture? Half the time, they’re guessing based on volume spikes and hoping the math works. It’s like tracking a fish in a hurricane with a flashlight.
Anand Makawana
March 21, 2026 AT 00:46 AMWhile the technical underpinnings of on-chain tracing are indeed robust, one must acknowledge the epistemological limitations inherent in heuristic clustering methodologies. Address reuse, common spend analysis, and clustering algorithms are statistically valid, yet they operate under the assumption of behavioral homogeneity - a fallacy when applied to heterogeneous actors across global socio-economic strata.
Furthermore, the deployment of AI-driven anomaly detection systems, while promising, introduces latent bias through training data sourced predominantly from Western regulatory frameworks, thereby marginalizing non-KYC-compliant, decentralized financial practices prevalent in emerging economies.
Misty Williams
March 22, 2026 AT 07:43 AMIt’s disgusting how people treat blockchain like a free-for-all playground while pretending they’re not being watched. You think using a new address every time makes you safe? Newsflash: if you’re transacting with an exchange that’s KYC’d, your entire wallet history is tied to your real identity. And you’re not ‘privacy-conscious’ - you’re just lazy about following the rules.
Anyone who thinks privacy coins are ‘freedom tools’ is delusional. They’re just enablers for scammers and child predators. I’m tired of people romanticizing criminal behavior because it ‘feels’ anonymous.
Sarah Terry
March 24, 2026 AT 07:08 AMFor regular users, the takeaway is simple: if you’re not using privacy tools, assume every transaction is visible. That doesn’t mean you’re guilty - it means you’re transparent.
And if you’re running a business? Start treating blockchain compliance like tax reporting. It’s not optional. The fines are real, the audits are coming, and regulators aren’t bluffing.
Shayne Cokerdem
March 25, 2026 AT 08:31 AMso like… uhh… the gov and big banks are watchin all ur crypto moves? yeah ok. but like… why do they care if i send 0.01 btc to my buddy for pizza? this is just creepy. like… my bank account? yeah fine. but crypto? it’s supposed to be free. ugh. i hate this.
kavya barikar
March 25, 2026 AT 16:42 PMThe transparency of blockchain is a double-edged sword. While it enables accountability, it also removes the possibility of financial dignity for those who operate outside institutional systems. We must ask: who benefits from this surveillance, and who bears the cost?
aravindsai pandla
March 26, 2026 AT 17:28 PMAddress clustering is powerful, but it’s not infallible. I’ve seen legitimate DeFi power users cluster dozens of wallets to manage gas costs and liquidity positions. To label them as ‘one entity’ is to misunderstand how advanced users operate.
Tools like Nansen are useful, but they’re not omniscient. The real danger is when regulators treat algorithmic clusters as legal proof of ownership.
namrata singh
March 28, 2026 AT 16:27 PMI’ve been reading this whole thing and I’m just… wow. I didn’t realize how much goes into tracking a single transaction. It’s like watching a detective movie, but real.
It’s scary how much data is out there. And yet… so many people still think they’re anonymous. I guess that’s the real lesson here - perception vs reality.
Andrea Zaszczynski
March 30, 2026 AT 08:58 AMYou know what’s wild? The fact that we’re even having this conversation. In 2025, we’re still arguing about whether blockchain should be private or not. It’s 2025. We have neural nets predicting crime before it happens. Why are we still stuck in ‘trust vs surveillance’ debates from 2017?
It’s not about privacy. It’s about control. And the people building these tools? They’re not cops. They’re investors. And they own the data.
Cordany Harper
March 31, 2026 AT 00:15 AMAs someone who’s lived in three countries and moved crypto between them, I’ve seen how messy cross-chain tracing gets. I once sent USDT from Solana to Polygon, then to Ethereum, then back to Solana. Took me 3 hours to trace it myself.
Tools help, but they’re not perfect. And honestly? If you’re trying to track someone who knows what they’re doing? Good luck. The real criminals? They’re not using Tornado Cash. They’re using custom smart contracts no one’s ever seen.
DarShawn Owens
March 31, 2026 AT 19:32 PMBig thanks for laying this out so clearly. I’ve been trying to explain this to my uncle who thinks crypto is ‘untraceable magic money.’ Now I can just send him this.
Also, the part about mixers being used in 18% of criminal flows? That’s wild. I always thought it was way higher. Shows how much of it is still just basic stuff - reusing addresses, not using privacy tools. Simple mistakes.
Andy Green
April 1, 2026 AT 22:41 PMOh wow, so now we’re giving taxpayer-funded tools to private corporations like Chainalysis? How convenient. Let me guess - they’re all owned by ex-CIA agents with ties to defense contractors?
And you call this ‘compliance’? This is digital apartheid. If you’re not KYC’d, you’re a suspect. If you’re from a ‘high-risk’ country? You’re guilty until proven innocent. This isn’t justice - it’s algorithmic colonialism.
Zion Banks
April 2, 2026 AT 03:06 AMThey’re not tracing criminals. They’re tracing dissent. You think the FBI cares about ransomware? No. They care about people buying Bitcoin to avoid bank seizures. They care about people in Venezuela, Iran, Ukraine - people using crypto to survive. This isn’t about crime. It’s about control. And soon, they’ll ban private wallets entirely.
Mark my words: in 2026, they’ll require every wallet to have a government ID attached. Welcome to the blockchain police state.
Pradip Solanki
April 3, 2026 AT 09:53 AMCommon spend analysis is outdated. Anyone with half a brain knows to split funds across 10 wallets with staggered timing. You think a 2025 thief uses the same pattern as 2019? Please. The tools are running on 2020 datasets. They’re already obsolete.
Brad Zenner
April 4, 2026 AT 08:49 AMOne thing everyone misses: tracing works best when you have a single point of entry - like a KYC’d exchange. Without that, you’re just guessing. Most private wallets? They’re invisible. The real power isn’t in the tools. It’s in the centralized choke points. And those are getting harder to find.
Tony Phillips
April 5, 2026 AT 02:36 AMFor anyone new to this: think of blockchain like a public library. Every book you check out is logged. You don’t have to give your name, but if someone sees you check out 5 books on hacking in a week, they might ask questions.
It’s not surveillance. It’s observation. The difference? You’re free to walk away. Just don’t be surprised if someone notices what you’re reading.
Abhishek Thakur
April 6, 2026 AT 21:43 PMMonero isn’t untraceable. It’s just harder. And harder doesn’t mean impossible. The real issue? Most users don’t even know how to use it properly. They send from a KYC’d wallet to a Monero one - and boom, the trail starts there. The tech is there. The users? Not so much.
Jackie Crusenberry
April 7, 2026 AT 10:00 AMSo basically, we’re all just being watched. Cool. Guess I’ll just stop using crypto. Who needs money anyway?