Imagine handing over cash for a coffee, only to have the barista realize ten minutes later that you handed them a photocopy of the bill. In the physical world, this is impossible. Paper money has texture, serial numbers, and, most importantly, it exists in one place at one time. But digital files? They are easy to copy. If I send you a photo, I still have the original on my phone. This fundamental difference between physical assets and digital data created a massive problem for early digital currency developers: how do you prevent someone from spending the same digital coin twice?
This is known as double-spending, which is the act of spending the same unit of digital currency more than once. It’s not just a technical glitch; it’s an existential threat to any monetary system. If users can duplicate coins, the supply becomes infinite, inflation skyrockets, and the currency becomes worthless. Bitcoin solved this with its blockchain technology, but attackers never stopped trying to break the system. Today, we’ll look at exactly how these attacks work, why they happen, and what keeps your crypto safe.
The Core Problem: Why Digital Money Needs a Ledger
To understand double-spending attacks, you first need to grasp why they are even possible. Physical cash relies on scarcity. There are only so many $20 bills printed. When you hand one to someone, you no longer possess it. Digital information, however, is non-rivalrous. You can email a file to a thousand people, and you still have the file. Early attempts at electronic cash failed because there was no central authority to say, "Hey, John already spent those credits."
Centralized systems like banks solve this by keeping a master ledger. Every transaction is checked against this database in real-time. If you try to spend money you don’t have, the bank says no. The problem with centralized ledgers is trust. You have to trust the bank not to make mistakes, not to be hacked, and not to freeze your account. Satoshi Nakamoto’s breakthrough with Bitcoin was removing the middleman. Instead of one trusted party, thousands of computers (nodes) maintain a shared ledger. This distributed consensus makes it incredibly hard for anyone to cheat without being caught.
However, this decentralized model introduces latency. When you broadcast a transaction, it doesn’t instantly appear on every computer in the network. It takes time to propagate. This delay creates a window of opportunity for bad actors. That’s where double-spending attacks come in.
Method 1: The Race Attack
The simplest form of double-spending is the Race Attack. As the name suggests, it’s all about speed. Here’s how it works in practice:
- You go to an online store to buy a rare collectible worth 1 BTC.
- You send a transaction paying the merchant 1 BTC.
- Simultaneously, you send another transaction sending that same 1 BTC back to your own wallet.
- Both transactions hit the network at almost the exact same time.
The goal here is confusion. Because the network is decentralized, different nodes might see the two conflicting transactions in different orders. Some nodes might accept your payment to the merchant, while others accept your refund to yourself. If the merchant ships the goods based on the first confirmation they see, but the network eventually settles on the transaction where you kept the money, the merchant loses everything.
Race attacks rely on low fees and fast propagation. By setting high transaction fees, you increase the chance miners will prioritize your legitimate-looking transaction. However, if you’re the attacker, you’re hoping the network is slow or congested enough that the conflict isn’t resolved quickly. This method is most effective against merchants who ship goods after seeing only zero or one confirmation. It’s a gamble, but it’s cheap to attempt.
Method 2: The Finney Attack
Named after Hal Finney, the first person to receive a Bitcoin transaction from Satoshi, the Finney Attack is more sophisticated. It requires the attacker to be a miner. Here’s the setup:
- Pre-mining: The attacker mines a block privately. Inside this block, they include a transaction sending coins from their address to themselves (or another controlled address).
- Hiding: They keep this block secret and do not broadcast it to the network yet.
- The Transaction: While mining continues, they go to a merchant and pay for goods using those same coins in a new, public transaction.
- The Reveal: Once the merchant accepts the payment and perhaps ships the goods, the attacker broadcasts their pre-mined block.
If the pre-mined block is accepted by the network, it invalidates the transaction sent to the merchant. Why? Because the coins were already spent in the private block. The merchant’s transaction now looks like it’s trying to spend coins that don’t exist. The attacker gets the goods and keeps the coins.
This attack is harder to pull off than a Race Attack because it requires significant hashing power. You need to be able to mine a block faster than the rest of the network combined can find a new block. On a network like Bitcoin, this is nearly impossible for an individual. But on smaller altcoins with lower hash rates, a single powerful miner could theoretically execute a Finney Attack repeatedly.

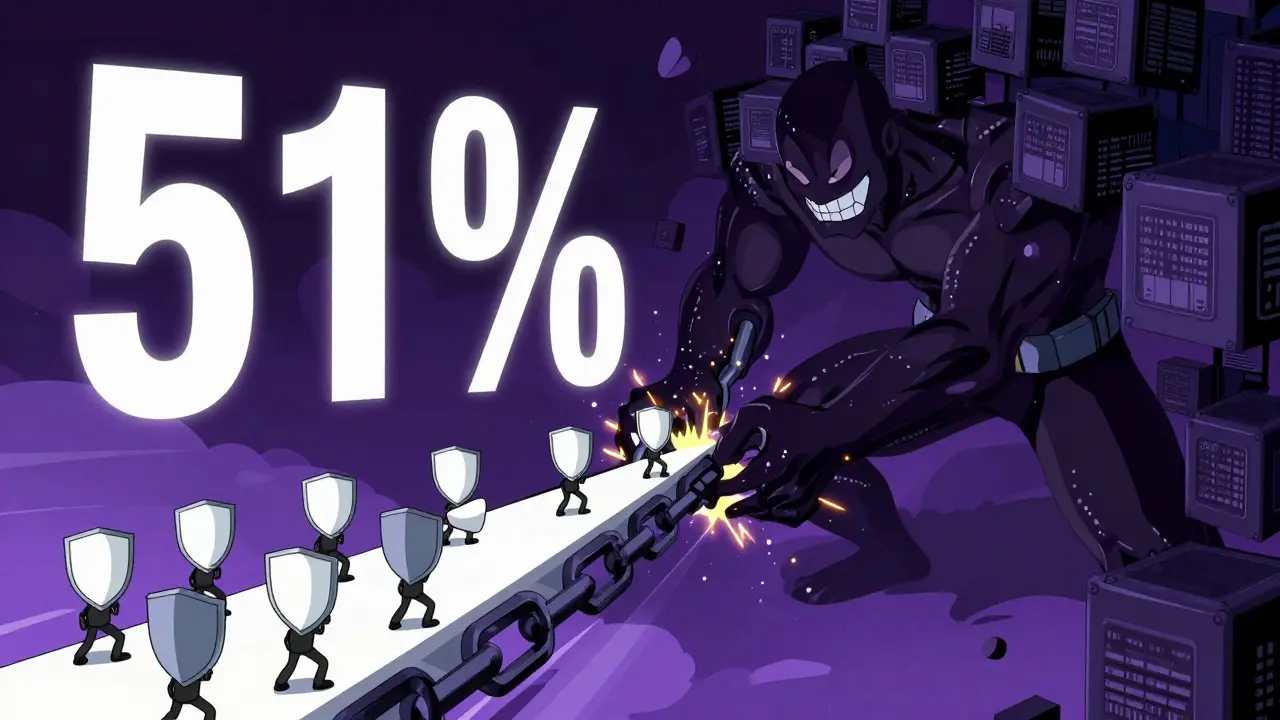
Method 3: The 51% Attack
The most devastating double-spending method is the 51% Attack. This isn’t just about confusing nodes; it’s about rewriting history. To execute this, an attacker needs to control more than 50% of the network’s total computational power (hash rate).
Here’s why 51% matters. In Proof-of-Work systems like Bitcoin, the longest chain is considered the true history. If you control the majority of the computing power, you can mine blocks faster than everyone else combined. This allows you to create a "private fork" of the blockchain.
- The attacker spends coins at a merchant.
- The merchant waits for confirmations (say, 6 blocks deep).
- Meanwhile, the attacker uses their superior hash power to mine a separate chain that excludes that transaction.
- Once the private chain is longer than the public chain, the attacker releases it.
- The network switches to the longer chain, effectively erasing the merchant’s transaction.
The result? The attacker has the goods and the coins. A 51% attack doesn’t just allow double-spending; it breaks the entire trust model of the blockchain. No transaction is safe until it’s deeply confirmed, and even then, a determined attacker with majority power can reverse it.
Bitcoin’s hash rate is currently over 400 exahashes per second. Controlling half of that would require billions of dollars in hardware and electricity costs, making it economically unfeasible for most attackers. However, smaller networks have fallen victim to this. Ethereum Classic, Bitcoin Gold, and Vertcoin have all experienced successful 51% attacks, resulting in millions of dollars in losses.
How Blockchain Prevents Double-Spending
So, if these attacks are so dangerous, why isn’t cryptocurrency collapsing under the weight of fraud? The answer lies in the design of the blockchain itself. Several layers of defense work together to make double-spending prohibitively expensive.
| Mechanism | Function | Security Level | Vulnerability |
|---|---|---|---|
| Cryptographic Signatures | Proves ownership of funds | High | Private key theft |
| Distributed Consensus | Agrees on transaction order | Very High | 51% Attack |
| Transaction Confirmations | Adds depth to the chain | Scales with depth | Time delay |
| Economic Incentives | Rewards honest behavior | High | Market crashes |
Cryptographic Signatures: Every transaction must be signed with a private key. This ensures that only the owner of the funds can authorize a spend. While this prevents unauthorized access, it doesn’t stop the owner from trying to spend the same coins twice. That’s where the next layer comes in.
Distributed Consensus: Nodes across the network validate every transaction. If a node sees a transaction spending coins that have already been spent in a previous block, it rejects it. This collective verification makes it hard for a single actor to lie about the state of the ledger.
Transaction Confirmations: This is your best practical defense. When a transaction is included in a block, it has one confirmation. Each subsequent block added on top increases the security exponentially. For Bitcoin, six confirmations are generally considered final. At this point, the amount of computational power required to reverse the transaction is astronomical. For small purchases, merchants might accept fewer confirmations to speed up service, accepting a slightly higher risk.
The Byzantine Generals Problem
To truly appreciate how blockchain solves double-spending, you have to look at the Byzantine Generals Problem. This is a classic thought experiment in computer science. Imagine several generals surrounding a city, each leading an army. They need to agree on whether to attack or retreat. They can only communicate via messengers, who might get captured or delayed. If some generals attack and others retreat, everyone loses.
In the context of cryptocurrency, the generals are the nodes, and the decision is the validity of a transaction. How do you reach agreement when you can’t trust the messengers (the network)? The solution isn’t perfect trust; it’s economic incentive. Miners are rewarded for following the rules and penalized for breaking them. If a miner tries to double-spend, they waste electricity and hardware costs for no reward. The system is designed so that honesty is the most profitable strategy.
Real-World Vulnerabilities and Smaller Networks
While Bitcoin is largely secure due to its immense hash rate, not all cryptocurrencies are created equal. Smaller networks with lower adoption and less computational power are vulnerable targets. We’ve seen multiple instances where attackers rented hashing power to perform 51% attacks on chains like Ethereum Classic and Litecoin.
These attacks often follow a pattern: the attacker buys the goods or exchanges the coins, then reverses the transactions once the exchange or merchant processes them. The loss isn’t just financial; it’s reputational. After a 51% attack, confidence in the affected network plummets, leading to price crashes and reduced usage.
This highlights a critical trade-off in blockchain design: decentralization vs. security. Highly decentralized networks are harder to attack but may be slower or more expensive. Centralized solutions offer speed and ease of use but reintroduce the single point of failure that blockchain aims to eliminate.
Protecting Yourself and Your Business
If you’re a user, double-spending is rarely your direct concern. Exchanges and wallets handle the complexity for you. However, if you’re running a business that accepts cryptocurrency directly, you need to be vigilant.
- Wait for Confirmations: Never ship high-value goods based on zero confirmations. Wait for at least three to six confirmations depending on the value and the specific cryptocurrency.
- Use Payment Processors: Services like BitPay or Coinbase Commerce monitor the network for suspicious activity. They can detect race attacks and alert you before you lose funds.
- Monitor Hash Rates: Be aware of the health of the network you’re accepting payments in. Sudden drops in hash rate can indicate vulnerability.
- Understand Layer-2 Risks: Solutions like the Lightning Network offer instant transactions but introduce new complexities. Ensure you understand the security model of any secondary layer you use.
For individuals, the main risk is interacting with shady exchanges or peer-to-peer platforms that don’t enforce proper confirmation standards. Always verify the reputation of the platform you’re using.
The Future of Double-Spending Defense
As technology evolves, so do the threats. Quantum computing poses a theoretical risk to current cryptographic signatures, potentially allowing attackers to forge keys. Researchers are already working on post-quantum cryptography to future-proof blockchains.
We’re also seeing a shift in consensus mechanisms. Proof-of-Stake (PoS) systems, used by Ethereum and others, approach double-spending differently. Instead of buying computing power, an attacker would need to acquire a majority of the staked tokens. This changes the economic calculus of an attack, making it potentially more expensive and visible. While PoS introduces different vulnerabilities, such as long-range attacks, it offers a robust alternative to energy-intensive Proof-of-Work.
Ultimately, the battle against double-spending is a continuous arms race. Attackers look for weaknesses in latency, code, and economics. Defenders respond with better algorithms, deeper confirmations, and stronger incentives. As long as cryptocurrency holds value, this dynamic will continue. Understanding these methods isn’t just for hackers; it’s essential knowledge for anyone participating in the digital economy.
What is a double-spending attack in simple terms?
A double-spending attack is when someone tries to spend the same digital coin twice. Since digital files can be copied easily, without a system to track ownership, a user could send the same coin to two different people simultaneously, causing both transactions to appear valid temporarily.
Can Bitcoin be double-spent?
Theoretically, yes, but practically, it is extremely difficult. Bitcoin’s network has a massive hash rate, making a 51% attack prohibitively expensive. While race attacks can occur with zero confirmations, waiting for six confirmations makes a double-spend virtually impossible.
What is the difference between a Race Attack and a Finney Attack?
A Race Attack involves sending two conflicting transactions simultaneously to confuse the network about which one is valid. A Finney Attack is more complex; it requires the attacker to be a miner who pre-mines a block with a self-payment, hides it, pays a merchant publicly, and then reveals the hidden block to invalidate the merchant's payment.
How does a 51% attack work?
In a 51% attack, an entity gains control of more than half of the network’s computing power. This allows them to outpace the rest of the network, creating a private version of the blockchain that excludes certain transactions. They can then release this longer chain, forcing the network to accept it and reversing previously confirmed transactions.
Why are smaller cryptocurrencies more vulnerable to double-spending?
Smaller cryptocurrencies have lower hash rates, meaning less computational power is securing the network. This makes it cheaper and easier for an attacker to rent or build enough mining equipment to perform a 51% attack compared to larger networks like Bitcoin.
How many confirmations should I wait for to avoid double-spending?
For Bitcoin, six confirmations are the standard for high-value transactions, providing near-total security. For smaller amounts, one to three confirmations may be acceptable, depending on your risk tolerance. Always check the specific recommendations for the cryptocurrency you are using.





